The usage of Whatsapp for OTP messages instead of SMSs is on the rise, with more businesses adopting WhatsApp OTP for verification with each new year. This is due to the enhanced security and faster delivery it provides, as well as the enhanced user experience that is achieved by making authentication more reliable.
WhatsApp OTP also ensures enhanced focus on encrypted communication and compliance. With this, cost reductions can be easily achieved. If you are considering WhatsApp OTP for your platform or not sure about its value, here are the key aspects you need to know.
A WhatsApp OTP is a time-sensitive verification code sent to a user in their WhatsApp chats. The primary objective is to confirm identity, authorize a login, reset a password or approve a transaction.
The WhatsApp OTP process typically involves generating a unique code by your backend system that is connected to Whatsapp Business API, and delivering it through WhatsApp's encrypted messaging app. This helps businesses verify users better more securely than with SMSs and reduce authentication delays.
The process of sending a WhatsApp OTP follows a clear, standardized flow designed for speed and security.
User Action Triggers Verification
A user begins an action such as signing in, creating an account, confirming a payment, or resetting a password. This prompts your system to request authentication.
Backend System Generates the OTP
Your authentication system creates a unique, time-bound code, usually valid for 30 seconds to a few minutes. Short validity helps reduce the risk of unauthorized reuse.
The OTP is Sent Through WhatsApp Business API
The OTP is placed inside an approved WhatsApp message template (templates are approved by meta to make sending messages from business to users stricter). Because WhatsApp enforces template approval, the format stays consistent, clear and compliant with regulations.
User Enters the OTP
The user opens their WhatsApp chat (by clicking the notification they receive), retrieves the code, and enters it into your app or site to complete verification. This process is familiar and straightforward for users.
OTP Expires Automatically
Once the time limit expires, the code becomes invalid and a new one must be requested if authentication is done already. This prevents misuse if a message is delayed or intercepted.
Through this practice, WhatsApp provides visibility through read receipts, strong encryption for secure delivery of the OTP message, and a familiar interface that users are used to.
Setting up WhatsApp OTP delivery requires several components that are set up at once. Here is what you need to setup:
A Verified WhatsApp Business Account (WABA)
Businesses must sign up for and verify a WhatsApp Business Account. Verification confirms your identity and activates your account, which means WhatsApp will display your business name to users and unlock higher messaging volumes. Still, at this point, you can’t use WhatsApp to send OTPs.
Access to the WhatsApp Business API
WhatsApp OTPs can only be delivered through the WhatsApp Business API, not the standard WhatsApp app. The API connects a system you use, whether it is your CRM or a dedicated WhatsApp tool, with WhatsApp's messaging infrastructure and allows automated, large-scale OTP delivery. Many companies obtain access to this API through official solution providers that handle onboarding, technical setup, and compliance requirements.
Pre-Approved OTP Message Templates
All WhatsApp messages must use templates approved by WhatsApp. For OTP messages, templates must show consistent formatting, clear placement for the dynamic OTP value and no promotional content. This prevents template message rejection and maintains a reliable delivery experience.
User Opt-In
WhatsApp requires explicit opt-in from users before you send an OTP message, or any other type of messages. Opt-ins can be collected during sign-up, checkout, or any onboarding step. Without clear consent from users, WhatsApp may restrict your account.
Secure OTP Generation and Validation
Your system must have the capability to generate time-sensitive codes, store them securely, validate them when entered and invalidate them once used or expired. This part of the process integrates directly with WhatsApp's delivery channel.
WhatsApp OTPs offer several advantages compared to other ways to send OTPs. Here are the most important benefits:
Faster Delivery and Enhanced Visibility
WhatsApp notifications typically appear instantly, and users are also used to opening the app quickly during daily communication. This reduces delays and increases the likelihood that users submit OTPs on time, improving overall verification from the first code success rates.
Stronger Security
WhatsApp protects messages with end-to-end encryption. The OTP is encrypted from the moment it leaves your system until the user reads it, making WhatsApp a more secure choice for sensitive verification compared to SMS and email.
Lower Costs in Certain Countries
In markets where SMS is relatively expensive or unreliable, WhatsApp OTP delivery can reduce verification costs. This helps businesses save money on authentication operations.
Verified Business Identity
Users instantly see who the OTP is coming from. Your business name and profile photo appear at the top of the chat, building trust and reducing the chance of phishing or spoofing.
More Reliable Delivery in Global Markets
WhatsApp bypasses issues such as SMS carrier outages, inconsistent international delivery or blocked messages. As long as the user has internet access, messages arrive reliably.
Better User Experience
WhatsApp is interactive, familiar, and widely used. Because users are already active in the app, verification feels effortless when done via WhatsApp.
Authentica offers WhatsApp OTP authentication that is pre-built and ready to integrate via the Authentica API. You can learn more about how Authentica guarantees smooth integration and secure WhatsApp OTPs by requesting a free consultation with our experts.
WhatsApp OTP plays a vital role in ensuring secure user verification and preventing unauthorized access. By combining encrypted delivery, global reach, and verified business identities, it improves both security and the user experience.
While SMS and email still play important roles as fallback options, WhatsApp is becoming the preferred channel for organizations seeking reliable, real-time authentication. Businesses that invest in WhatsApp OTP gain faster verification, better security, and enhanced customer trust in an increasingly digital environment.
Protecting identities, user and enterprise sensitive information is becoming more complicated than ever, especially with the ongoing AI boom. Traditional password-based verification methods, while more familiar and seem to be an easier option for many users, have been proven to be vulnerable to many attacks and errors.
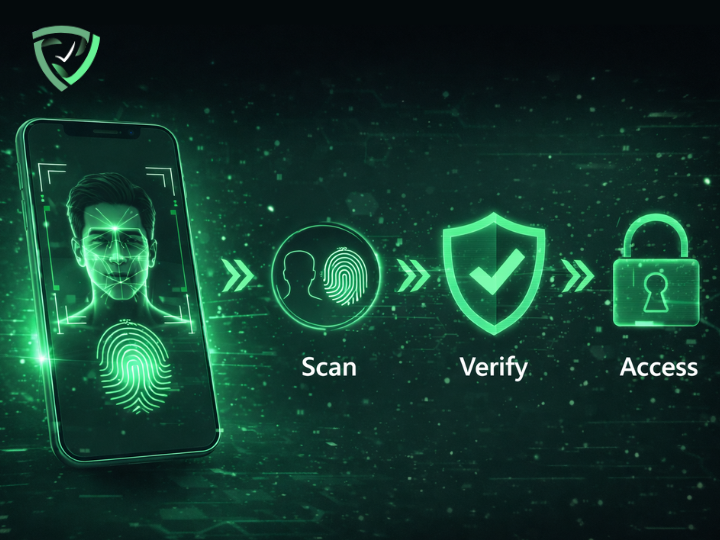
Biometric authentication offers an alternative to passwords and more vulnerable authentication methods, as users verify identity through unique traits rather than something users have to remember or carry that can be stolen.
In this blog, we will explore what biometric authentication is, how it works, the main types of biometric authentication, and when to use them.
Biometric authentication is a security process that confirms a person’s identity by analyzing their unique biological traits like fingerprints, facial features or voice. These characteristics are captured and stored and compared to the user input each time they authenticate.
Unlike passwords or tokens that can be stolen or forgotten, biometric identification is unique to each person and nearly impossible to replicate accurately. This makes biometric authentication both highly secure and convenient and this is why it is now widely used in verifying online transactions, unlocking smartphones and even granting physical access to highly secured facilities.
Biometric authentication comes in many forms, each with its unique advantages and suitable applications. Understanding these types helps organizations choose the right mix of authentication methods to use, depending on their industry and user needs and preferences.
Fingerprint authentication analyzes the unique fingerprint patterns on a fingertip using optical, capacitive, or ultrasonic sensors. It is one of the most common and cost-effective biometric authentication methods, widely used in smartphones to authenticate apps and unlock the phone itself, in addition to access control and attendance management systems.
With facial recognition, the user face is mapped and key facial features are analyzed, such as the distance between eyes or the contour of the jawline, to create a mathematical representation of a face that is stored and later compared while logging in.
It offers quick, contactless verification and is commonly used for smartphone security, airport check-ins, and corporate access systems.
These methods analyze the unique patterns in a person’s eyes, more specifically the iris or the retina. Both are highly accurate and ideal for environments that demand top-level security, such as border control and government systems.
Voice authentication identifies a user by analyzing vocal characteristics such as pitch, tone and cadence. It’s particularly effective and widely used for phone banking, virtual assistants, and call center verification.
This category includes gait recognition (how a person walks), typing rhythm, and even mouse movement patterns in some advanced applications. It enables continuous authentication, monitoring users passively while they interact with systems to detect anomalies or unauthorized access.
Vein recognition is another biometric authentication method that uses infrared light to map the unique pattern of veins in a person’s hand or fingers. Similarly, hand geometry measures finger length and palm structure. Both methods are mostly suited to secure facility access and can be used in other healthcare applications.
Biometric authentication is increasingly adopted across industries because it provides a strong balance of security, efficiency and user convenience, which are the main factors that define which authentication methods are used to secure devices, facilities or user accounts. These are the biggest benefits of using biometric authentication instead of other traditional authentication methods:
Biometric traits are unique and difficult to counterfeit, making them highly resistant to attacks such as phishing or credential theft. The reliance on biological features rather than knowledge-based credentials significantly reduces the risk of unauthorized access, which is one of the biggest and most clear benefits.
With biometric authentication, users no longer need to remember or reset complex passwords every time they open one of their accounts. A fingerprint scan or facial recognition takes seconds, enabling fast authentication with unmatched convenience compared to any other type of authentication.
While initial setup costs for biometric authentication methods, especially advanced ones like face recognition, can be higher than traditional systems, biometric authentication reduces ongoing expenses tied to password management, recovery and the amount of support provided. Over time, this translates into substantial savings for organizations.
For industries governed by strict regulations, such as finance or healthcare, biometric authentication helps meet compliance standards like Know Your Customer (KYC), Anti-Money Laundering (AML), and different data protection laws by ensuring strong, verifiable identity checks that are in many cases obligatory.
Although biometric authentication can be applied broadly, its adoption can be more beneficial for specific industries, where it adds the most value. Here is where biometric authentication shines most:
Sectors such as defense and government benefit from the heightened security biometrics offer, minimizing risks associated with credential-based breaches that can’t be afforded.
Hospitals can use biometric authentication methods like fingerprint and iris recognition to ensure accurate patient identification and protect confidential health records.
Banks and fintech platforms adopt biometric authentication for seamless, secure verification in mobile banking, transaction confirmation and call centers.
Airports and immigration systems use facial recognition and iris scanning to speed up passenger processing while maintaining security integrity.
Mobile apps now use biometric authentication widely for unlocking apps, authorizing purchases and orders and protecting personal accounts.
Implementing biometric authentication from scratch can be complex, requiring deep expertise in security, user experience and system integration. Authentica simplifies all of this with a readily developed biometric authentication API, bringing facial recognition, fingerprint matching and voice verification. Developers can easily access this API on platforms like **[RapidAPI]**, and an **[n8n node]** is available for integration into automation workflows, without building them internally and wasting money and resources. You can get in touch with our team to learn more.
Biometric authentication represents a major step forward in the evolution of digital authentication for devices and accounts. It combines security, convenience and speed in a way that traditional methods cannot match. From securing financial transactions to enhancing healthcare systems and mobile experiences, biometrics are redefining online security, especially with the ability to integrate it widely with tools like Authentica.

Voice authentication has rapidly emerged as a reliable way to verify identities in online apps and smart devices, simply through people’s unique voices. This technology combines biometrics with AI-driven precision, creating a secure and seamless experience across various devices and industries.
In this article, we’ll explore what voice authentication is, how it works, its key benefits and limitations, and how you can implement it easily through Authentica, a leader in digital identity solutions.
Voice authentication, also called voice verification, is a type of biometric authentication that uses a person’s unique vocal characteristics to confirm their identity. Just as fingerprints or facial features can serve as identifiers, a person’s voice offers distinctive physiological and behavioral traits that are difficult to replicate.
When a user first enrolls in a system, their voice is recorded through a first time setting process known as voice enrollment. This involves capturing multiple samples of speech to form a reference model, which is often called a voiceprint or more professionally, enrollment template. Once these samples are stored securely, this template becomes the base for verification whenever it is needed.
During authentication, the system compares a new sample of the user’s voice against the stored template. Advanced algorithms analyze multiple vocal features, such as tone, pitch, cadence, and pronunciation, to determine if both samples match.
There are two primary types of voice authentication:
Voice authentication can be deployed across a range of applications including mobile banking, call centers, web platforms, and IoT devices, offering flexible, hands-free verification wherever needed.
Voice authentication’s wide implementation is because of its balance of security, simplicity and scalability. Businesses across industries are trusting it as a tool to strengthen customer trust while making interactions faster and more seamless. These are some of the benefits of voice authentication technology:
Unlike passwords or PINs that can be stolen, voice biometrics are tied to the user’s unique biological identity. Every human voice is shaped by over 70 unique physiological factors, from vocal cord length to sinus cavity shape, making it highly resistant to duplication.
When combined with liveness detection and device-based verification, voice authentication offers multi-factor security that effectively mitigates risks of widely used attacks like phishing and social engineering.
Voice authentication removes the burden of remembering complex passwords or verifying through multiple manual steps. A quick spoken phrase or even a short conversation can authenticate the user without hassle, creating a smoother experience that boosts satisfaction.
In call centers, verifying customers traditionally requires agents to ask multiple security questions, a process that consumes time and increases costs. With voice authentication, the system can identify callers automatically, cutting down Average Handle Time (AHT) and freeing agents to focus on resolving issues rather than verifying identity.
Because voice authentication is contactless, it offers accessibility advantages for users who may find other authentication methods harder to use. It also minimizes physical contact, a benefit that became especially relevant during the COVID-19 pandemic.
While voice authentication brings clear advantages, it doesn't come without challenges. Businesses adopting this technology should understand its potential limitations to design a balanced security approach:
Voiceprints, like any digital data, must be stored securely. If breached, unlike passwords, a compromised voice cannot simply be “reset.” Therefore, strong encryption and secure storage practices are essential.
Background noise or poor audio quality can reduce accuracy. Environments like busy offices or public areas may not always be ideal for voice verification, requiring additional backup options.
A cold, sore throat, or even emotional stress can alter vocal tone enough to affect verification accuracy. While advanced systems can tolerate minor variations, extreme cases may require alternative authentication methods.
Modern voice technologies can imitate speech patterns with incredible precision . However, top-tier systems now integrate anti-spoofing AI and liveness detection to identify synthetic or replayed voices. Maintaining this technological edge requires constant updates and testing.
For organizations aiming to integrate voice authentication without building everything from scratch, which can be hard or time-consuming especially with such technology needing continuous updates in the era of AI, Authentica offers a streamlined solution.
Authentica provides AI-driven biometric identity authentication API, allowing businesses to deploy these technologies with no coding or development and with guaranteed updates and a pay as you go pricing model. You can learn more at authentica.sa or leave questions here.
Voice authentication is no longer futuristic, it’s practical, scalable and already shaping how users access services securely. By using a reliable technology that addresses challenges like spoofing and inaccuracy, a great user experience and security balance can be provided.

Data breaches and online fraud are increasingly common, and One-Time Password (OTP) verification has become an essential concept in online security. It’s the extra layer of protection that ensures user accounts are not accessed by someone else, whether logging into an account, completing a transaction, or recovering a password.
OTP authentication, or One-Time Password authentication, involves sending users a temporary, unique code to confirm their identity and prevent unauthorized access by hackers or other people with malicious intents. Because these codes are valid for only one session or a brief amount of time, they prevent attackers from reusing stolen credentials like passwords.
This makes OTP verification one of the simplest yet most effective tools for strengthening security in apps, websites, financial platforms, and government systems.
Beyond basic login protection, OTP plays a key role in two-factor authentication (2FA), combining something the user knows (a password) with something they receive (the OTP). It also supports passwordless authentication and helps businesses comply with KYC (Know Your Customer) and KYB (Know Your Business) regulations through timestamped verification logs.
One-Time Password (OTP) verification can be delivered through several channels, each offering distinct advantages in terms of speed, reliability and user experience. Choosing the right method depends on the nature of the transaction or protected account, the target audience, and the level of security required. These are the different available channels for sending OTPs:
Each method has its own strengths, and many organizations combine multiple channels to provide both reliability and user choice. A multi-channel OTP strategy not only strengthens security but also enhances user trust by ensuring codes are always accessible.
OTP verification is used across industries to build trust and protect users. It plays an essential role in:
Authentica’s developer-friendly API enables OTP verification with no development effort, and with the easiest possible integration and a pay-as-you-go model to pay only on-demand. This allows you to comply with standards, get to the market faster and reduce initial costs drastically.
OTP verification remains one of the most reliable methods for protecting user identities and securing online transactions. The growing demand for multi-channel, scalable, and regulation-compliant solutions make it an essential method of verification. By adopting flexible and well-integrated OTP systems, organizations can strengthen trust, reduce fraud, and deliver safer digital experiences, and all of this can be used without any effort with a readily developed API like the one provided by Authentica.
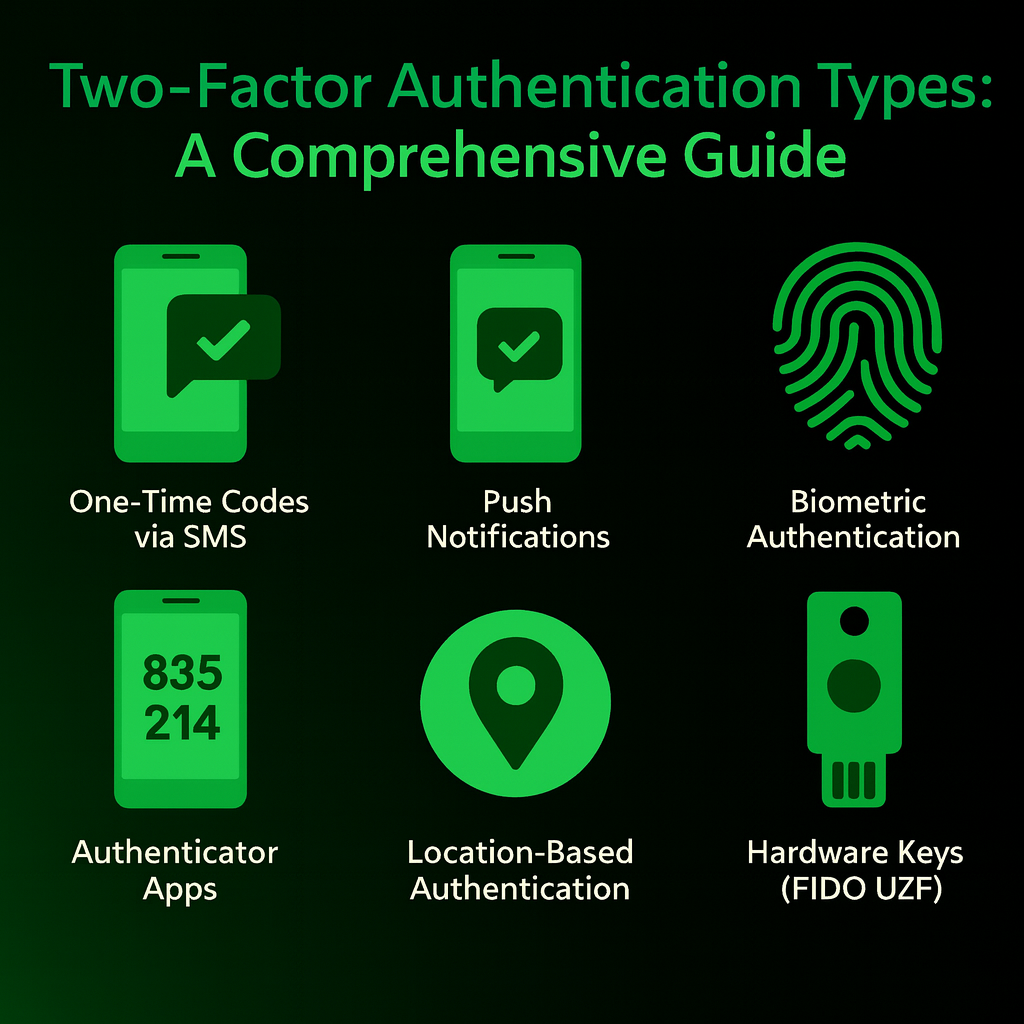
Two-factor authentication (2FA) has become essential for digital security, as it offers a robust way to protect user accounts from unauthorized access. For developers building applications, integrating 2FA is no longer optional. It's a necessity to ensure user trust and data safety. In this article, we’ll break down what 2FA is, explore its different types, guide you on choosing the right options for your app, and discuss the benefits of using a third-party vendor like Authentica.
Two-factor authentication is a security mechanism that requires users to verify their identity using two different ways before accessing an application or a platform. Unlike relying only on a username and password, 2FA combines something the user knows (like a password) with something they have (like a phone or a fingerprint).
This dual-layer approach significantly reduces the risk of account compromise, even if a password is stolen. By adding this extra step, 2FA makes it much harder for cybercriminals or people with malicious intents to hijack accounts through phishing or brute-force attacks.
There are several 2FA methods, each with its own strengths and weaknesses. Below, we outline the most common options to help you understand their practical applications.
One of the most widely used 2FA methods involves sending a one-time code to a user’s phone or email. This code is called one time code or one time password (OTP). The user enters this unique code to verify their identity. SMS is the most popular delivery method, but voice calls or email are also widely used.
Pros: Relatively easy to implement and widely accessible, as most users already have a phone or email account.
Cons: SMS and voice calls are vulnerable to SIM-swapping or interception, and email-based codes offer limited security if the email account uses the same password as the primary account. Losing access to a phone number can also lock users out.
Push notifications send a login approval request to a user’s trusted device through a notification from an app, allowing them to approve or deny access by clicking the notification.
Pros: User-friendly and fast, requiring no code entry. Reduces phishing risks compared to SMS.
Cons: Requires an app on the user device. Can be vulnerable to accidental approvals if users aren’t cautious.
Apps like Google Authenticator or Microsoft Authenticator generate codes that are valid for a few seconds on the app on a user’s device, eliminating the need for network-based delivery. These codes vary by platform, so every service has its forever-changing unique code that changes every few seconds.
Pros: More secure than SMS, as codes are generated offline and harder to intercept. Works without mobile network access.
Cons: Requires users to install and manage an app, and losing the device can lead to lockout if not backed up properly.
Biometric methods, such as fingerprint or facial recognition, use a user’s face or fingerprint scan to get them through their accounts.
Pros: Extremely convenient, requiring no manual input.
Cons: Biometric data is sensitive and unchangeable, raising privacy concerns.
Location-Based Authentication
Location-based authentication usually serves as an implicit authentication factor, and is often used by services to flag logins from unexpected places.
Pros: Runs in the background, requiring no user action unless a login attempt is flagged.
Cons: Not highly reliable on its own, as IP-based location can be manipulated, and multiple users may share the same location.
Hardware keys, like YubiKey or Google Titan, use cryptography to authenticate both the user and the service, protecting against man-in-the-middle attacks.
Pros: A very secure 2FA method, resistant to phishing and interception. Simple to use, with just plug in or tap via NFC.
Cons: Expensive to distribute at scale, and keys can be lost or damaged.
Some services, like in Google accounts, provide users with a list of pre-generated one-time codes for authentication or transaction verification.
Pros: Highly secure due to their randomness and rarity of transmission, making interception difficult.
Cons: Storage is a challenge, as codes must be kept in a secure location,
Password as a Second Factor
In some cases, a password serves as the second factor. This is often seen in messaging apps like WhatsApp or Telegram. Here, a one-time SMS code acts as the first factor, and an optional password provides additional security.
Pros: Protects against loss of phone number access.
Cons: Relies on users setting strong, unique passwords, which isn’t always guaranteed.
Selecting the right 2FA methods for your application depends on your user base, security requirements, and any operational constraints. Here are key factors to consider:
Implementing 2FA from scratch can be complex, requiring expertise in cryptography, user management, and compliance. This is where third-party vendors like Authentica come in, especially with its Saudi market focus and expertise. Authentica provides pre-built 2FA solutions that integrate seamlessly with your application, saving time and reducing errors, so that you can focus on your app’s core functionality while outsourcing the complexity of secure authentication.
Two-factor authentication is a critical tool for safeguarding user accounts in an increasingly threat-filled landscape. By understanding the strengths and weaknesses of each 2FA method, whether it’s SMS, authenticator apps, biometrics, or hardware keys, you can make informed decisions about what to offer in your platform. Balancing security, usability, and cost is key, and using a trusted service like Authentica can simplify the process while ensuring robust protection.

In our rapidly evolving digital world, cybersecurity has become a top priority for individuals and businesses alike. With increasing threats and breaches, traditional passwords are no longer sufficient to provide the necessary protection. This is where the One-Time Password (OTP) comes in—a simple yet highly effective security technology that has revolutionized how we secure our accounts and digital transactions.
A One-Time Password (OTP), also known as a One-Time PIN, One-Time Authorization Code, or dynamic password, is an automatically generated alphanumeric code valid for a single login session or transaction [1]. Unlike static passwords that can be reused repeatedly, an OTP loses its validity immediately after use or after a very short period, making it a strong shield against many cyberattacks.
Imagine you are trying to log in to your online banking account. After entering your username and static password, the system asks you to enter an additional code sent to your mobile phone or email. This code is the OTP. Even if an attacker manages to steal your username and password, they will not be able to access your account without the unique OTP generated at that specific moment.
The mechanism of OTP relies on a simple yet powerful principle: generating a unique code for each verification process. When a user requests an OTP, the system generates this code using complex algorithms and then sends it to a trusted communication channel owned by the user, such as their mobile phone via SMS or WhatsApp, or their email. Once the user receives the code, they enter it into the system to complete the verification process.
There are two main types of OTPs:
1.Time-based One-Time Password (TOTP): These codes are valid for a very short period, usually 30 or 60 seconds. They are generated using an algorithm that combines a shared secret key and the current time. This is the most common type used by authentication apps like Google Authenticator.
2.HMAC-based One-Time Password (HOTP): These codes rely on a counter that increments with each use. The code is generated using a shared secret key and the counter value. Each time a code is used, the counter increases, ensuring that the next code will be different. This type is less common in daily use but equally effective.
Several reasons make OTP a fundamental component of modern security strategies:
•Protection Against Password Theft: Even if attackers manage to obtain your static password through phishing, malware, or data breaches, they will not be able to access your account without the real-time generated OTP.
•Combating Replay Attacks: Since each OTP is valid only once, attackers cannot intercept the code and reuse it later for unauthorized access.
•Enhancing Trust and Security: OTP provides an additional layer of security, reassuring users that their accounts and transactions are well-protected. This builds trust in digital services and increases adoption rates.
•Compliance with Regulatory Standards: Many industries, such as financial services and healthcare, require high levels of security and identity verification. OTP helps companies comply with these regulations and standards.
•Ease of Use: Despite its technical complexity, OTP is easy for the end-user to use. All it requires is entering a code consisting of a few digits or characters, which is a quick and intuitive process.
Authentica understands the importance of providing robust and flexible verification solutions to meet diverse business needs. For this reason, Authentica offers a comprehensive suite of multi-channel OTP solutions, ensuring that businesses can secure their operations and authenticate their users with confidence and ease. Authentica is a product of T2, a leading company in providing innovative technical solutions.
Short Message Service (SMS) is one of the most common and reliable methods for sending OTP codes. This method is widely adopted, as most people own mobile phones and can easily receive text messages. Authentica offers an SMS OTP solution that ensures fast, secure, and highly reliable delivery of codes. Whether you need two-factor authentication (2FA), phone number verification during registration, or account recovery, Authentica's SMS OTP provides the ideal solution. The solution boasts industry-leading delivery rates (99.9%+) and transfer times faster than a second, supported by a redundant global infrastructure. It also allows you to use your own sender ID and branded templates to enhance trust and provide a professional experience.
With the growing popularity of WhatsApp as a primary communication platform, sending OTP codes via WhatsApp has become an attractive option for many businesses. Authentica's WhatsApp OTP provides a secure and familiar way for users to receive verification codes. Codes are sent directly via WhatsApp using an officially approved sender name, which enhances your brand identity and gives the user a smooth and reliable experience. This solution features seamless integration, secure messaging with end-to-end encryption, and the use of a familiar channel that users already trust. This solution is ideal for businesses that want to reach their customers through their preferred channels.
Despite the emergence of new channels, email remains an effective and reliable method for sending OTP codes, especially in cases such as account registration, password recovery, and sensitive operations. Authentica's Email OTP provides a reliable and flexible solution for sending verification codes to user emails with messages that carry your brand identity. This solution features professional, customizable email templates, sending using a trusted sender domain, local and international delivery support, and accurate reports to track delivery and open rates. Authentica's Email OTP ensures fast delivery consistent with your brand identity, enhancing the verification experience and providing professionalism without complexity.
•Multi-Channel Verification from One Place: Authentica provides a unified platform for user verification via SMS, WhatsApp, and email, in addition to extra tools like biometric verification .
•Tailored Solutions for Every Sector: Whether you operate in financial and tech services, e-commerce, health and education, or government and law, Authentica offers customized solutions that precisely meet your sector's needs.
•Easy Integration for Developers: Authentica's solution features quick technical integration via clear API interfaces, making it suitable for startup teams and large organizations.
•Real-time Visibility and Full Control: You can monitor every verification attempt in real-time, with tracking of sending and response status, and built-in alternative options.
•Scalability with High Security: From hundreds to millions of users, Authentica ensures performance and compatibility at every level, while maintaining the highest security standards.
To further streamline integration and workflow automation, Authentica provides its own plugin for the popular automation platform N8N. This integration allows developers and businesses to easily connect Authentica's services with hundreds of other applications and services, opening new possibilities for seamless automation and verification. You can find Authentica's N8N plugin
In an era of increasing cyber threats, One-Time Passwords (OTP) have become an indispensable tool for enhancing digital security. By providing an additional layer of protection, OTP helps individuals and businesses protect their accounts and transactions from unauthorized access. Authentica, as a product of T2, offers multi-channel OTP solutions (SMS OTP, WhatsApp OTP, Email OTP) that combine strong security with flexibility and ease of use, making it the ideal partner for any company seeking to enhance its digital security and customer trust.